Vulnerability in Cyber Security - A Step-by-Step Guide for Beginners
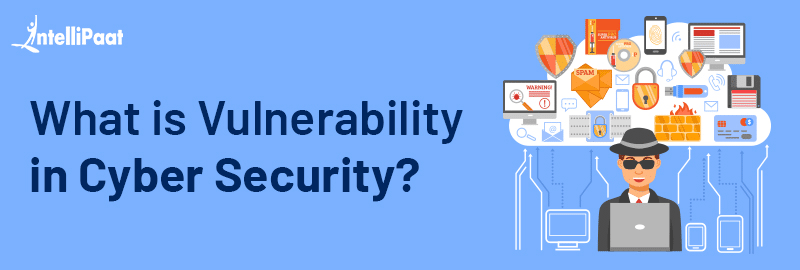
Vulnerability Remediation Process - 4 Steps to Remediation
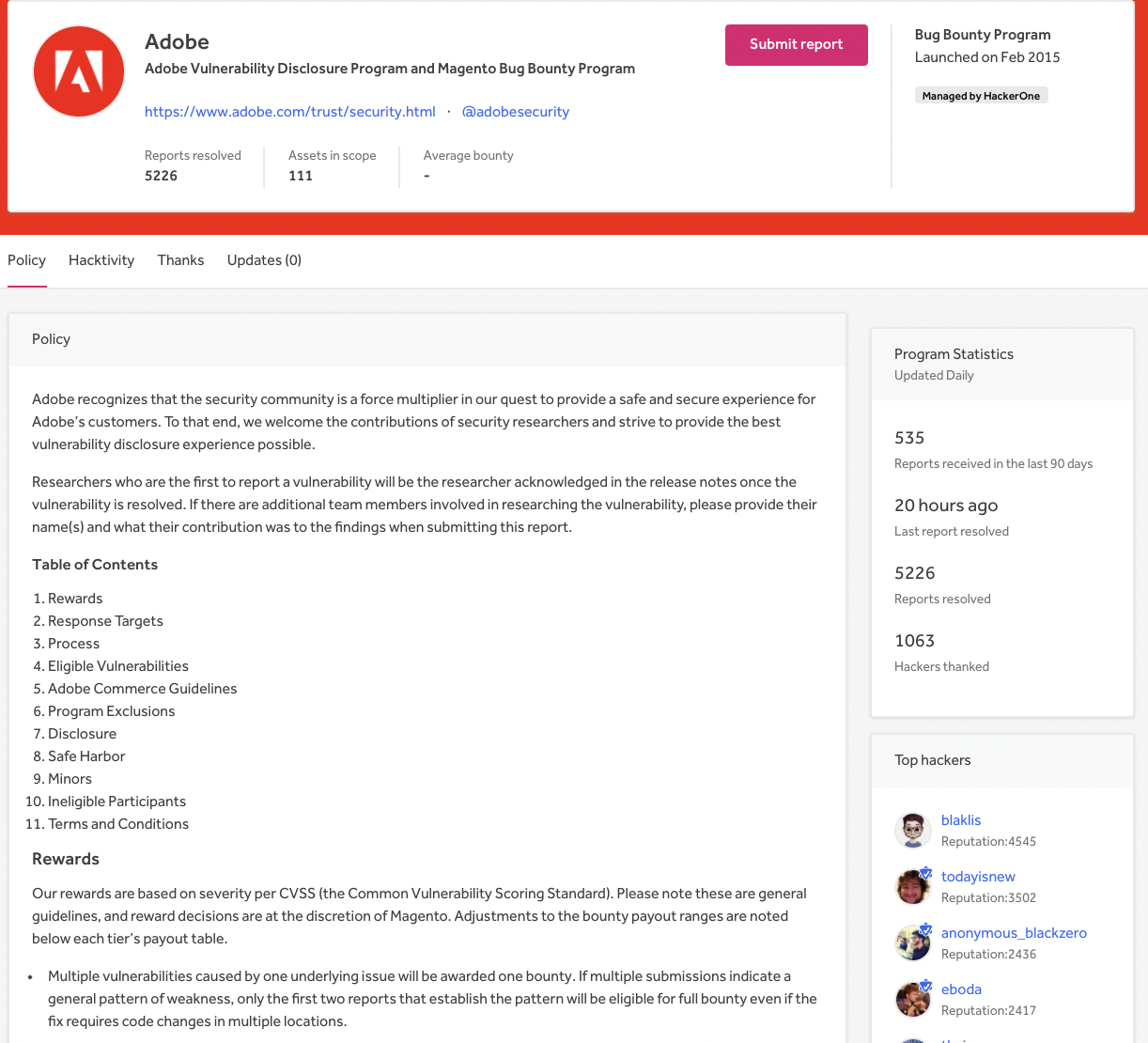
Bug Bounty vs. VDP, Which Program Is Right for You?
Tale of a Windows Error Reporting Zero-Day (CVE-2019-0863)
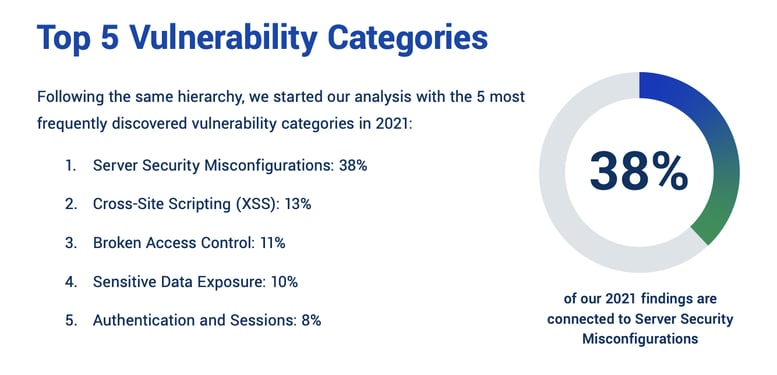
Top Cybersecurity Statistics to Know for 2023

Log4J Vulnerability Explained: What It Is and How to Fix It

Report Components HackerOne Platform Documentation
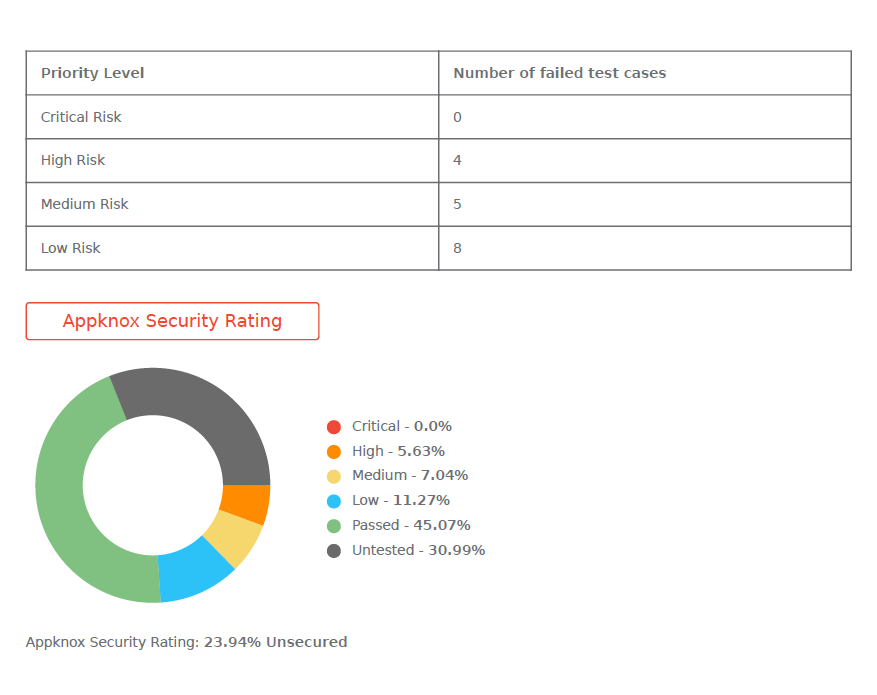
What to Look in Mobile App Security Assessment Report

Git security vulnerabilities announced - The GitHub Blog

How To Perform A Vulnerability Assessment: A Step-by-Step Guide

Meltdown (security vulnerability) - Wikipedia